Inbound Email Security
Stop the full spectrum of email threats with behavioral AI that knows your people.
AI-powered Attacks Are Evolving Faster Than Defenses
Costly
The average business email compromise attack costs organizations $137,132.
Frequent
4,000% increase in phishing volume since the introduction of generative AI tools.
Difficult to Detect
86% of business leaders report at least one AI-related security incident in the past year.
How Abnormal Stops the Full Spectrum of Email Attacks
Learns Good Behavior to Stop the Bad
Traditional security memorizes known indicators. Abnormal models what normal looks like. Through a one-click API integration, the platform analyzes identity, context, and communication signals together to surface subtle deviations—detecting advanced threats such as BEC, VEC, malicious calendar invites, and coordinated impersonation campaigns that rule-based defenses miss.
Fully Automates Threat Prevention and Response
Abnormal automatically detects and remediates malicious messages before users can engage. Customers block dozens of BEC attempts per month, see up to 4x fewer inbox threats, and save 15+ hours per week through autonomous protection—shifting from reactive triage to proactive risk reduction.

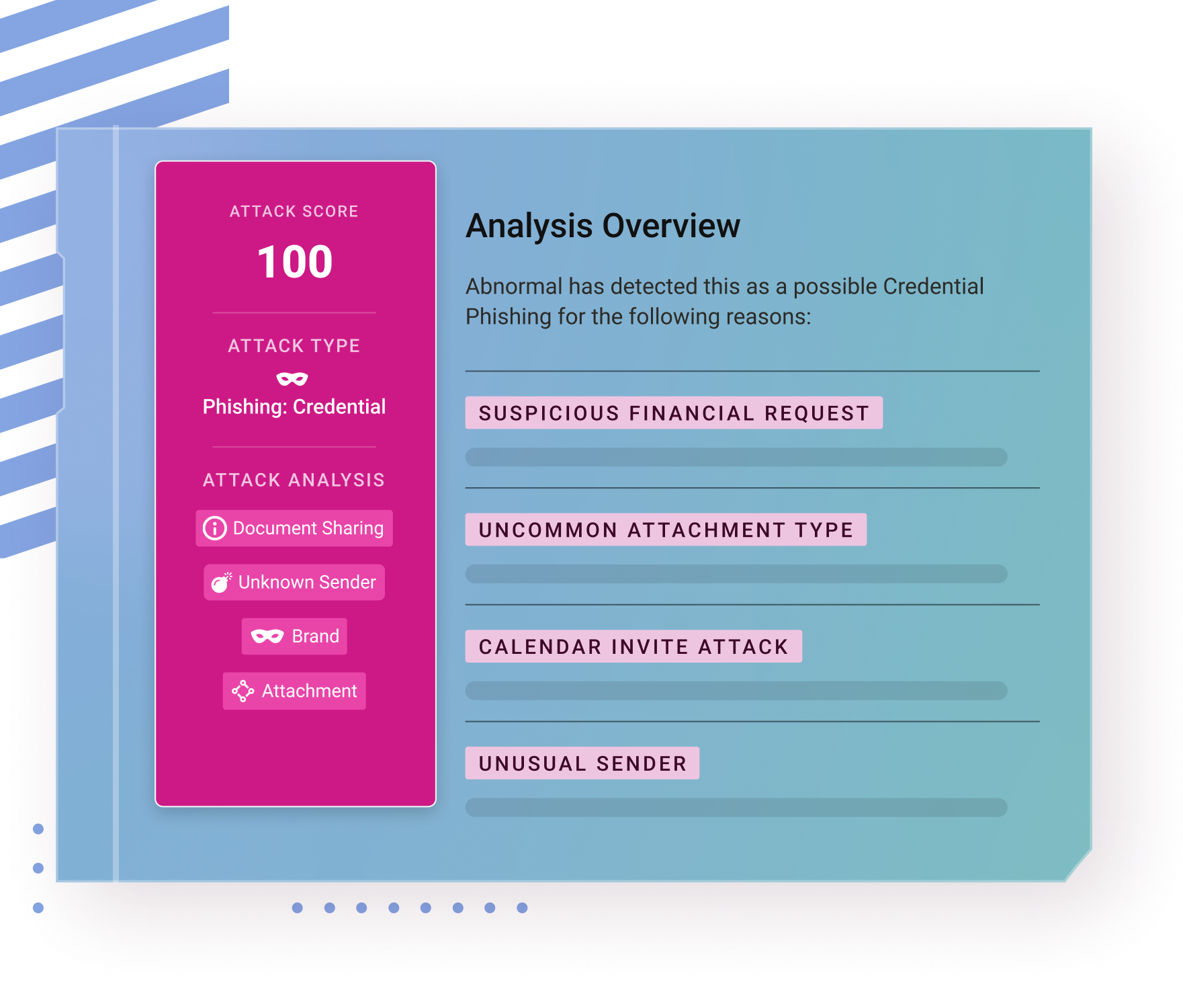
Delivers Explainable Outcomes and Comprehensive Visibility
Every threat stopped is backed by clear, contextual evidence enriched with behavioral signals that explain the verdict and the associated risk. Analysts can investigate detection rationale, trace anomalous behaviors, and search historical events through detailed logs and visual timelines—all within a unified console.

Enables Custom Controls Without Complexity
Remediation and quarantine workflows are tailored to organizational needs without brittle rules or policy sprawl. Quarantine Release brings Microsoft-quarantined emails into Abnormal’s Search & Respond for unified bulk triage and release, while URL Rewriting reduces exposure to risky links. A unified interface consolidates detections and integrates with SOAR tools to streamline response.

Continuously Learns and Adapts to Emerging Threats
Powered by behavioral AI, Abnormal continuously evolves by learning from user behavior, attack trends, and cross-tenant intelligence. It detects never-before-seen threats without relying on static IOCs or signatures, and requires no manual tuning, rule writing, or policy maintenance. Detection evolves with changing threats while remaining transparent to security teams.

See How Inbound Email Security Works
BEC Detection
Human Behavior AI
VEC Detection
The realization of value was almost immediate—real-time visibility into attacks going on in the environment that are bypassing the traditional defenses. That context allowed ADT to start identifying threat trends while blocking them from employee inboxes.”
The realization of value was almost immediate—real-time visibility into attacks going on in the environment that are bypassing the traditional defenses. That context allowed ADT to start identifying threat trends while blocking them from employee inboxes.”