How Cybersecurity Mesh Architecture Enables Behavioral AI at Scale
Discover how cybersecurity mesh architecture enables composable security while behavioral AI fills critical detection gaps in distributed environments.
January 31, 2026
Cybersecurity mesh architecture has become the preferred framework for integrating security tools across distributed enterprise environments. The approach enables composability, allowing organizations to build unified security operations from disparate technologies without replacing existing investments.
For security leaders managing cloud-native infrastructures, hybrid workforces, and expanding SaaS ecosystems, CSMA solves the interoperability problem.
What CSMA doesn't solve is detection. The framework coordinates tools and orchestrates responses, but it cannot identify threats on its own. As attackers shift tactics toward credential-based compromise and social engineering, the detection layer requires intelligence that understands behavioral context, not just threat signatures.
The architecture is only as effective as the security technologies operating within it, which raises a critical question for enterprise security teams: what type of threat detection actually works at scale across a distributed mesh?
What Is Cybersecurity Mesh Architecture?
CSMA enables disparate security tools to function as a unified framework without requiring wholesale technology replacement. ScienceDirect research validates that CSMA delivers scalability, flexibility, composability, robustness, and resilience, providing independent academic validation beyond analyst perspectives.
Core Principles of CSMA
CSMA operates on three foundational principles that address critical enterprise security challenges:
Composability: Organizations can integrate disparate security tools into a unified framework without wholesale technology replacement, creating architectural flexibility to leverage existing investments through API-based integration.
Scalability: The architecture extends security controls across distributed assets, supporting enterprise growth, cloud adoption, and distributed workforce models without requiring linear expansion of tools or headcount.
Interoperability: CSMA allows the interoperability and coordination between intelligent security systems, enabling unified security data sharing and coordinated threat response.
CSMA aligns conceptually with NIST Zero Trust Architecture standards in Special Publication 800-207. Both frameworks eliminate implicit trust based on network location and implement identity-centric security controls.
The Four Layers of Cybersecurity Mesh Architecture
CSMA organizes security capabilities into four foundational layers that enable unified threat detection and response. Each layer enables specific security functions while maintaining interoperability with the others.
Security Analytics and Intelligence
Security analytics and intelligence provide the data foundation for detecting threats across distributed environments. This layer aggregates and correlates security events through SIEM and XDR solutions. By centralizing analysis, organizations can identify patterns across distributed environments that would remain invisible to siloed security tools.
Distributed Identity Fabric
The distributed identity fabric enables consistent authentication regardless of where users, devices, or applications reside. This layer supports zero trust architecture principles and provides the authentication and authorization infrastructure necessary for modern hybrid and multi-cloud environments where assets exist outside traditional network boundaries.
Consolidated Policy and Posture Management
Consolidated policy and posture management enables centralized policy creation with distributed enforcement across the security mesh. Organizations define security policies once and enforce them consistently across the mesh, including support for Policy as Code approaches for automation.
This layer also encompasses security posture management, ensuring configurations across cloud environments align with security requirements.
Consolidated Dashboards
The consolidated dashboard layer provides unified visibility and management interfaces across the distributed security mesh. Security operations teams gain centralized views into threat activity, policy compliance, and security posture without switching between multiple tool-specific interfaces, reducing operational complexity and supporting executive reporting requirements.
Why Behavioral AI is Critical for CSMA Security Analytics
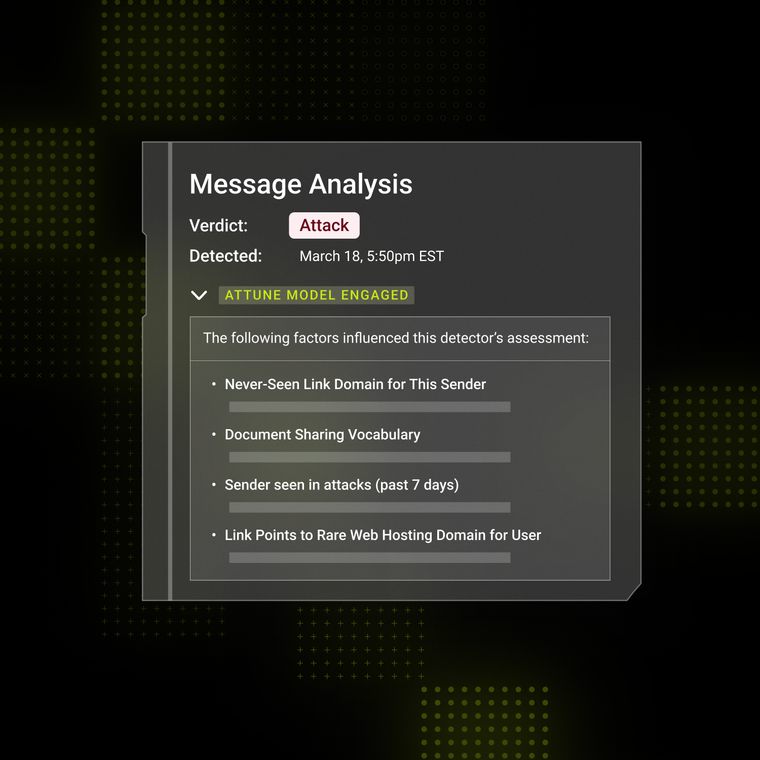
The security analytics layer requires behavioral AI to detect email threats that signature-based tools often miss. Traditional email security typically generates alerts based on known threat patterns; behavioral AI identifies anomalies by understanding what normal communication looks like.
Signature-based detection requires previous observation and signature creation before threats can be identified. These traditional approaches often struggle to identify credential-based attacks where threat actors use the same authentication mechanisms as legitimate users.
A SANS case study in May 2024 demonstrated this gap: when attackers used valid stolen credentials, signature-based tools had no detection surface because there were no malicious attachments, URLs, or authentication failures. Security teams detected the attack only through an unusual inbox rule change: a behavioral anomaly that signature-based systems cannot identify.
Business Email Compromise, Account Takeover, and Vendor Email Compromise attacks all leverage compromised credentials to access email accounts directly. Attackers trigger no signature-based detection when they access accounts using valid credentials, create inbox rules to redirect correspondence, and modify banking instructions.
These threats require behavioral analysis to detect anomalous authentication patterns, login timing, geographic anomalies, and behavioral changes after access.
How Behavioral AI Integrates Across CSMA Layers
API-based behavioral AI, such as Abnormal, integrates with CSMA's composable security model, providing threat intelligence across all four architectural layers. Rather than requiring infrastructure changes or complex deployment projects, behavioral AI platforms connect through standard APIs to enhance each layer's capabilities while maintaining the architectural flexibility that makes CSMA effective.
Security Analytics Integration
Behavioral AI sends detections directly to security analytics platforms through standard API integrations, enriching SIEM data with behavioral context that signature-based tools cannot provide.
When Abnormal detects anomalous email activity, such as unusual sending patterns, atypical communication relationships, or suspicious content characteristics, relevant telemetry flows to SIEM platforms like Microsoft Sentinel through Azure Event Hubs or REST webhooks.
This integration enables composable deployment without infrastructure changes. Security teams gain behavioral intelligence within their existing analytics workflows, correlating email-based threats with network, endpoint, and cloud security events for comprehensive threat visibility.
Identity Fabric Correlation
Behavioral AI correlates email threat detection with identity provider data from Okta integration and Azure AD, creating a unified view of user behavior across authentication and communication channels. When email behavior deviates from identity baselines, like a user suddenly communicating with unfamiliar external contacts or sending messages at unusual times, enriched alerts with full context reach security teams.
This correlation incorporates authentication context and identity risk signals, enabling security teams to identify account compromise scenarios where attackers use valid credentials but exhibit behavioral patterns inconsistent with the legitimate account owner.
Policy Management Automation
Behavioral AI detections inform automated remediation through policy management integrations, reducing response time from hours to seconds. When Abnormal identifies a compromised account or malicious message, automated workflows can quarantine suspicious messages, initiate password resets for compromised accounts, or trigger identity verification challenges, all without manual intervention.
This automation aligns with CSMA's consolidated policy management layer by enabling security teams to define response policies once and execute them consistently across the mesh based on behavioral AI intelligence.
Dashboard Enhancement
Abnormal's AI Data Analyst enhances the consolidated dashboard layer by transforming raw security data into actionable intelligence. Rather than requiring security teams to manually correlate data across multiple interfaces, the AI Data Analyst enables natural language queries to investigate threats, surface relevant context, and identify patterns across the email environment.
Security teams can generate executive-ready reports on threat trends, measure detection efficacy, and benchmark performance against industry trends, providing the visibility that security leaders need to demonstrate value and identify improvement opportunities.
Behavioral AI Makes Cybersecurity Mesh Architecture Effective
Cybersecurity mesh architecture enables composability, scalability, and interoperability of security tools across distributed enterprises. Behavioral AI provides the threat detection intelligence that identifies anomalies and deviations from normal communication patterns that signature-based systems often miss.
Cloud-native email security architectures built on behavioral AI deliver what CSMA frameworks need most: intelligent threat detection that adapts to evolving attack patterns while integrating seamlessly with existing security investments. This approach fills the critical detection gap in distributed environments where credential-based attacks bypass traditional signature-based tools.
See how Abnormal transforms your security mesh from a coordination framework into an active defense system. Book a demo.
Related Posts
Get the Latest Email Security Insights
Subscribe to our newsletter to receive updates on the latest attacks and new trends in the email threat landscape.