Tycoon2FA Rebounds Post-Takedown with 6 Layers of Obfuscation
Twenty days after Europol seized 330 Tycoon2FA domains, a new campaign emerged with rebuilt infrastructure and six layers of obfuscation. Here's how it works.
May 6, 2026
/
8 min read

Key Findings
A new Tycoon2FA deployment was identified operating from freshly registered Russian infrastructure, 20 days after the March 4, 2026, coordinated takedown that seized 330 domains.
The campaign uses AWS S3-hosted lure pages, a nulled link management platform as an additional redirect layer, and dual fake CAPTCHA gates before delivering an encrypted credential harvesting payload.
Six layers of obfuscation protect the AiTM (adversary-in-the-middle) relay engine, including a polymorphic Caesar+XOR cipher seeded by a linear congruential generator—the same obfuscation fingerprint found in confirmed pre-takedown Tycoon2FA deployments.
Kill switch infrastructure has migrated from Cloudflare to BunnyCDN, a direct response to the takedown’s targeting of Cloudflare-hosted C2 domains.
The campaign was confirmed active on April 2, 2026, with kill switches returning live responses and credential harvesting endpoints accepting form submissions.
Background: The Tycoon2FA Takedown
On March 4, 2026, Europol, Microsoft, and law enforcement partners disrupted the Tycoon2FA phishing-as-a-service platform, which was responsible for an estimated 62% of adversary-in-the-middle (AiTM) phishing attacks blocked by Microsoft in early 2026. The operation seized 330 domains and targeted Cloudflare-hosted infrastructure used by Tycoon2FA operators. However, CrowdStrike reported that operators began rebuilding within the same day.
Less than three weeks later, a new campaign emerged with the same encryption fingerprint, the same anti-analysis suite, and infrastructure rebuilt from scratch. This investigation documents this rebuild in detail.
The Attack Chain
Tycoon2FA uses a seven-stage attack chain with redundant anti-analysis at every step. The design is deliberate: each stage independently prevents security tools and researchers from reaching subsequent stages, meaning that no single layer of the chain can be inspected in isolation without bypassing the layers before it.
Stage 1: S3-Hosted Lure
The attack begins with a cloned Microsoft Power Pages portal hosted on an AWS S3 bucket. The page impersonates a OneDrive file-sharing notification: “You have received files from a member of External Client Share for your review” with a procurement lure—“RFQ/#PO Enquiry - Microsoft Spreadsheet.”
The Power Pages template (v9.7.3.10) was cloned from a real Azure tenant provisioned in the Saudi Arabia region, giving the page authentic Microsoft framework code, telemetry scripts, and styling. A setTimeout fires after 3 seconds, redirecting the victim to the next stage.
S3 hosting is a deliberate choice: S3 bucket URLs carry AWS domain reputation and bypass many URL reputation checks that would flag a freshly registered domain.
Stage 2: Link Management Platform
The second stage adds a layer of separation between the initial lure and the phishing destination, making it harder for email security tools to connect the link a target clicks to the page that ultimately harvests their credentials.
The redirect lands on a 66biolinks instance—a commercial link management platform (by AltumCode) running as a pirated copy on attacker-controlled infrastructure. This layer serves two purposes: an additional redirect hop that hides the final destination from email gateway URL scanners, and URL shortening and tracking for the operator.
The platform runs on LiteSpeed with CyberPanel on an IPXO-leased IP (212.81.47.99), fronted by Cloudflare. The domain uses a randomized name to avoid pattern-based blocking.
Stage 3: IP Blocklist Gate
Stage 3 filters out security researchers, automated scanners, and cloud-hosted analysis tools before they ever see the phishing content—ensuring that only real targets reach subsequent stages.
Before showing any phishing content, JavaScript queries ipinfo[.]io to check the visitor’s IP organization. If the organization matches any of 16 cloud and hosting providers, the visitor is redirected to a rotating set of legitimate ecommerce platforms: volusion[.]com, prestashop[.]com, ecwid[.]com, squareup[.]com. This makes the redirect appear like normal browsing rather than a suspicious dead end.
To evade static string scanning, the cloud and hosting provider names are stored with the brand name spelled backward, as shown in the table below:

Stage 4: Dual Fake CAPTCHA Gates
Visitors that pass the IP check are presented with a fake “Human Check” verification page—a checkbox with four animated progress bars and a “Verification Successful” confirmation message. This is not a real CAPTCHA service; it is a Tycoon2FA-specific gate template documented by Bridewell as appearing in January–February 2026 variants.
The campaign uses two sequential CAPTCHA gates—one on the link management platform, and one on the credential harvesting domain (criopiochio[.]ru). This introduces redundancy into the attack chain, ensuring that even if one layer is bypassed or flagged, subsequent stages continue to filter automated analysis and delay investigation.
Both share the same UX but with polymorphic CSS class names: the first uses .r0, .w2, .of4 while the second uses .o0, .f7, .ru2. Form IDs, checkbox IDs, and variable names all differ between renders, but the algorithm and structure are identical. This means the two gates look the same to a target but appear as different code to security tools that rely on signature matching.
The hidden form uses HTML entity obfuscation for its method attribute: method="P& #79;S& #84;" decodes to “POST.” On submission, the first CAPTCHA redirects (301) to criopiochio[.]ru; the second triggers the encrypted payload delivery.
Stage 5: Encrypted Payload
After the second CAPTCHA, the server returns an obfuscated JavaScript payload that is decrypted and executed on the client side. The encryption uses a custom scheme based on a Linear Congruential Generator (LCG) with specific constants—multiplier 9301, increment 49297, modulus 233280—that serve as the stable cryptographic fingerprint of Tycoon2FA. These constants remain identical across all observed deployments to date, including confirmed pre-takedown domains (freasiju[.]ru, edistolygrag[.]ru) and this post-takedown campaign.
The encryption scheme layers multiple techniques in sequence. The payload is formatted as three colon-separated components—base64_payload : seed_integer : base64_key—and the decryption chain proceeds as follows:
Generate XOR keystream using PRNG seeded from seed + decoded_key[0]
Generate Caesar shift values using PRNG seeded from seed + 99
Reverse Caesar cipher on alphabetic characters using per-position shift values
XOR each byte with the corresponding keystream byte
Execute the result via eval.
New in This Variant
In addition to the core encryption scheme, this campaign introduces new techniques to disguise how the decrypted payload executes JavaScript functions.
The eval function is invoked indirectly through frames["eval"] via a Symbol.toPrimitive trick, and the string “eval” is extracted from the first characters of CSS color-like values (#e64D00 → ‘e’, #v05235 → ‘v’, #a0B100 → ‘a’, #l2C3D4 → ‘l’), which are not valid hex colors but are used purely for character extraction. Similarly, atob is constructed via XOR: [0x63, 0x66, 0x61, 0x66] ^ [0x02, 0x12, 0x0e, 0x04].
This level of layered, reusable obfuscation shows that Tycoon2FA is not a commodity kit, but a maintained platform engineered to evade modern detection, where static signatures and simple pattern matching are no longer effective.
Stage 6: Anti-Analysis Suite
The decrypted payload contains an extensive anti-analysis suite that executes before any credential harvesting:
Automation detection: The payload checks for indicators of automated browsing and analysis tools, such as navigator.webdriver, window.callPhantom, window._phantom, and “Burp” in the user agent string. Any match redirects to about:blank.
DevTools blocking: To prevent manual inspection of the page's code, all keyboard shortcuts for developer tools are intercepted and suppressed—e.g., F12, Ctrl+U, Ctrl+Shift+I/C/J/K, Cmd+Alt+I/C. The right-click context menu is also disabled.
Continuous debugger trap: A setInterval loop executes a debugger statement every 100 milliseconds. If DevTools is open, the debugger pause introduces a measurable delay detected via performance.now() timing. When triggered, the page redirects to a rotating ecommerce decoy site.
Platform blocking: Linux desktops (excluding Android) are blanked entirely with document.write(""). This specifically targets security researchers, who commonly use Linux workstations for malware analysis.
Domain-Level Deception
In addition to the payload-level controls above, every route on the phishing domain returns a different AI-generated fake website—a hallmark of Tycoon2FA. Analysts, URL scanners, and reputation services that probe the domain see a completely different, benign-looking site, depending on how they access it.


Screenshots of fake, AI-generated redirect destinations
Collectively, these controls indicate a shift from passive evasion to active counter-analysis, where the goal is not only to avoid detection but to disrupt tooling, waste analyst time, and create blind spots in automated inspection systems.
Stage 7: Kill Switch and Credential Harvesting
Before rendering the credential harvester, the payload checks a remote kill switch. A GET request is sent to a C2 domain. If the response is "0", the campaign is active; any other value or error triggers a redirect to a benign site.
Two kill switch domains were identified: founiodrai[.]digital and ziostohou[.]digital, both hosted on BunnyCDN (84.17.63.178). This represents a deliberate shift from the Cloudflare infrastructure that was seized in the March 4 takedown. Operators diversified their CDN provider to reduce reliance on a single provider and complicate future coordinated disruption efforts.
When the kill switch confirms the campaign is active, the deobfuscated JavaScript POSTs to a randomized endpoint with two parameters: bltpg (a campaign/page identifier) and sid (a per-session token). The server responds with {"status":"success"} and the page reloads to deliver the AiTM credential harvesting page. This page acts as a real-time proxy to the Microsoft login flow, capturing credentials and session tokens as the target authenticates on Microsoft's legitimate infrastructure.
Detection and Mitigation
The indicators and techniques identified in this investigation provide several opportunities for defenders to detect and disrupt this campaign, as well as strengthen defenses against AiTM attacks more broadly.
Block or alert on the kill switch domains.
founiodrai[.]digitalandziostohou[.]digitalare active C2 endpoints. Blocking these causes the campaign to self-deactivate for your users.Hunt for
bltpgparameter in proxy/WAFPOSTlogs. This is a Tycoon2FA-specific parameter not used by legitimate applications.Enable Conditional Access policies restricting sign-ins from unfamiliar locations immediately after AiTM token capture. Because AiTM attacks capture session tokens in real time, restricting where those tokens can be used limits an attacker's ability to replay them.
Deploy token protection (token binding) for critical applications. This ensures that captured tokens cannot be used from a different device or location than the original authentication, preventing session token replay.
What Persists After the Rebuild
The March 2026 Tycoon2FA takedown disrupted but did not eliminate the platform. Within three weeks, operators rebuilt with adapted infrastructure—BunnyCDN replacing Cloudflare for kill switches, S3 lure pages adding redirect layers, and more aggressive anti-analysis (100ms debugger traps vs. 1000ms pre-takedown).
The core cryptographic fingerprint remains unchanged: the same LCG constants, the same Caesar+XOR cipher, the same bltpg kit parameter. This stability is the campaign’s weakness—it provides a reliable detection signal that persists across infrastructure changes.
Tycoon2FA's return demonstrates how quickly mature phishing operations can adapt, replatform, and resume activity after coordinated disruption. The infrastructure is disposable; the cryptographic identity is not. For as long as that remains true, defenders have a reliable signal to track this platform regardless of how many times its operators rebuild around it.
For additional insight into the attack landscape, visit Abnormal Intelligence, our threat intelligence data and research hub.
Indicators of Compromise
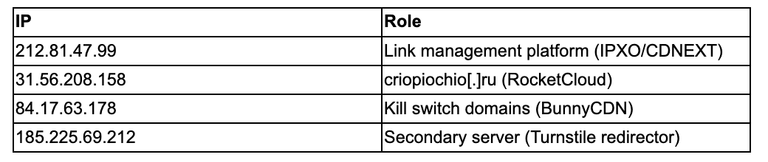
Domains
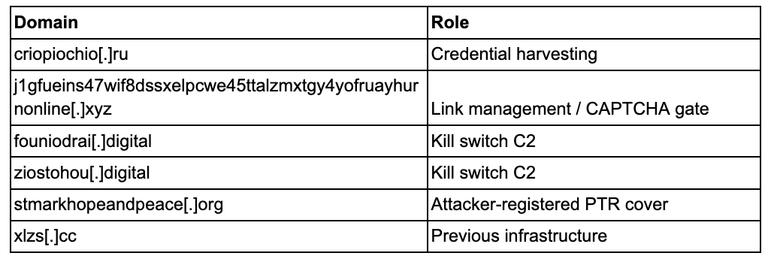
IP Addresses
S3
9zaeto0la2z7mdtvcg8zhilom4y7r53tw36esjgrifet62smtvojkgdgdyw.s3.us-east-2.amazonaws[.]com
Azure Tenant (from cloned Power Pages)
f657b565-2762-43b0-9a00-39ad751ad541 (Region: Saudi Arabia)
Related Posts
Get the Latest Email Security Insights
Subscribe to our newsletter to receive updates on the latest attacks and new trends in the email threat landscape.


