When Every Attack is a Novel Attack, You Need a New Kind of Defense
Abnormal introduces Attune 1.0, new visibility and control capabilities, and advances in human risk management, marking the next evolution of behavioral security.
March 17, 2026
/
5 min read

Communication is how we build trust. But that trust is being weaponized. Attackers aren't breaking in. They're blending in.
AI-assisted, hyper-realistic attacks are here. They execute without a human in the loop. They’ve scaled beyond what a human team can triage. And they’re designed to look different from the last attack. Signature-based detection was effective when "bad" had a recognizable shape. When every attack against you is new, the rules you write to stop them decay quickly. The only durable way to catch a threat actor behaving badly is to know what normal behavior looks like.
Traditional security memorizes IOCs to tag and stop known bad attacks. From the beginning of Abnormal AI, we believed a different approach was required. We made the bet that normal behavior, not threat intelligence, would become the most durable defense against evolving attacks. We built an AI-native detection engine capable of learning behavior by correlating tens of thousands of signals derived from each organization’s native email environment. Those normal baselines allowed our detection engine to precisely pinpoint anomalies. Eight years later, thousands of organizations trust us to protect users against the attacks they’ve seen already, and those they can’t imagine yet. Along the way, we’ve remained relentlessly obsessed with efficacy and precision. We learn from every user report, and launch frequent model improvements to customers.
Today I’m excited to introduce the culmination of eight years of relentless refinement: Attune 1.0, a behavioral foundation model trained on more than 1 billion derived behavioral signals. It already powers 85% of attack detections across the Abnormal Behavior Platform. Attune stops more attacks—especially the most sophisticated, most costly attacks—with less noise. It’s already detecting 150K more unique attack campaigns per week and operating with 50% higher precision than previous models.1
But there’s more. Along with Attune, we’re introducing new features to help security teams build customized detection models without relying on brittle rules, plus new training capabilities to help prepare employees for real attacks.
The pace at which threats evolve has always outrun the pace at which security companies could respond. But today, advances in AI-native software development are shortening security response cycles. Abnormal is at the forefront of this evolution. Building on an AI-native foundation changes how fast we can ship what's next. Today, our AI is safely designing, writing, and testing code. Our top AI agent now contributes nearly twenty times1 as much code as our most productive human engineer. In our experience, that allows us to go from a customer signal to a researched solution, fully implemented change, and an exhaustive test suite in a fraction of the time it used to take.
This AI-native velocity brings us to today, with powerful innovation going into RSAC 2026.
Attune 1.0: The Behavioral Foundation Model for Cybersecurity

Organizations are facing AI-powered attacks that rarely reuse infrastructure, payloads, or language. Point solutions and rule stacks struggle because they don’t baseline against how each organization normally behaves.
With Attune 1.0, we’re consolidating Abnormal’s behavioral understanding into a foundation model that unifies identity, behavior, and content signals across the Abnormal Platform. Attune gives security teams stronger detection with fewer false positives and protection that improves without manual rule-tuning.
Attune represents 8+ years of accumulated learning. What differentiates it from previous approaches is its unified multimodal architecture. Earlier detection systems often treated identity, behavior, and content as separate signals, evaluating them independently or combining them through heuristics. Attune learns these modalities jointly in a single transformer-based system, helping it understand how signals reinforce or contradict one another. This interaction learning brings structure to ambiguous signals and helps reveal patterns attackers work hardest to hide.
Vendors often tout the efficacy of their models with numbers, but what matters is outcomes: the attacks you repeatedly predict and prevent.
One example of an outcome unlocked by Attune is the prevention of a massive campaign of Microsoft Teams OAuth phishing attacks. Attune stopped a novel Microsoft Teams OAuth phishing campaign delivered through calendar invitations two months before external threat researchers even documented the pattern publicly1, blocking abused calendar invites and malicious OAuth consent flows before they became widely known. The attack did not need a known bad IP, a malicious URL, or a recognized payload for Attune to stop it. It just needed to be abnormal.
Attune 1.0 is Generally Available and powering Inbound Email Security attack detection for all Abnormal customers today.
Deeper Visibility and Fine-Tuned Control for Inbound Email Security
Security teams shouldn't have to choose between using AI and understanding how it works. At the same time, they want the option to shape detections based on local patterns, without falling back into brittle rules. To meet that need, we’re expanding Inbound Email Security with two capabilities: Detection 360 Insights and Custom AI Models.
Detection 360 Insights

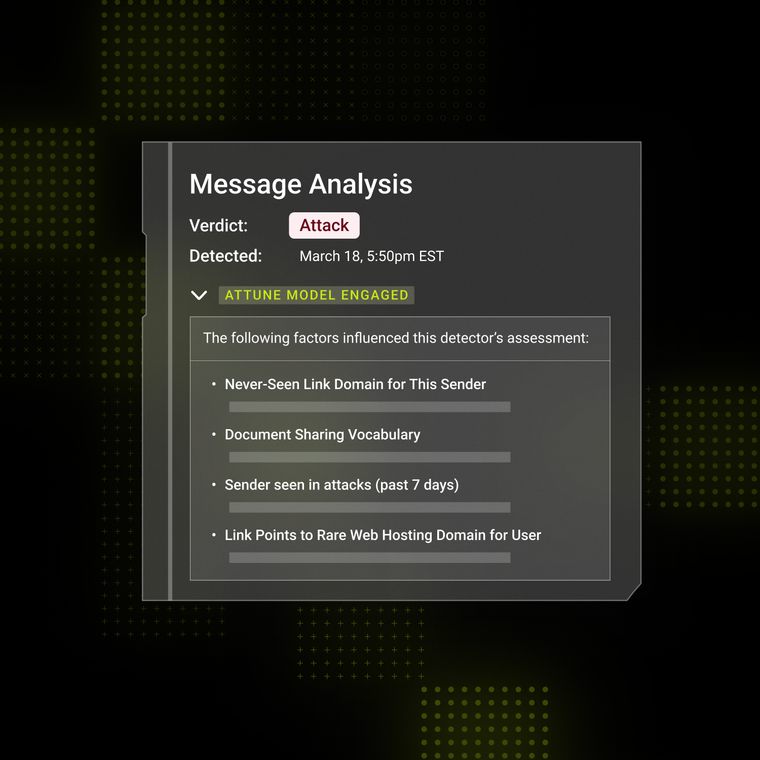
Detection 360 Insights (Generally Available) gives security teams visibility into the identity, relationship, and contextual signals that influenced a classification. Today, when analysts submit False Positives and False Negatives to Detection 360, AI can automatically triage the report, reclassify the message, and remediate impacted messages. With new insights, teams can see the step-by-step timeline and transparent reasoning behind each classification. This visibility can reduce investigation friction, accelerate resolution, and build confidence behind detection decisions.
Custom AI Models

Custom AI Models (Early Access) provide precise control without the need for hard-coded rules. Some organizations need the ability to flag messages that follow linguistic patterns without resorting to deterministic rules. Now, with a single example and a short description, analysts can define email patterns to tag and track. Abnormal's behavioral AI adapts to each organization through baseline learning. Custom AI Models, when enabled, apply local context directly into detection. The result is customized precision that is designed to strengthen over time.
Custom AI Models is available as a no-cost feature in Early Access for most Abnormal Inbound Email Security customers today, and Detection 360 Insights is Generally Available in the Abnormal portal now.
AI Phishing Coach: Automating Human Risk Management
Detection alone cannot solve the human risk problem. Employees remain the primary target for social engineering, and traditional security awareness training—often built with generic simulations and compliance-focused approaches—fails to drive meaningful behavior change.
AI Phishing Coach replaces this one-size-fits-all compliance training with an automated, AI-driven system that helps turn real-world threats into personalized coaching. Today we’re introducing two new capabilities to help security teams gain a continuously updated view of human risk posture without manual burden.
Phishing Risk Scoring

AI Phishing Coach now provides a regularly updated phishing-readiness measure through Phishing Risk Scoring (Generally Available), helping administrators measure the impact of training with behavior-based metrics. A unique per-user score, visible to authorized admins, is calculated based on criteria like simulation interactions, reporting activity, and training outcomes, and new reporting dashboards help track how the organization’s awareness is trending over time.
BEC and VEC Simulations
New, realistic BEC and VEC simulations (Generally Available) in AI Phishing Coach mirror organizational data and executive, colleague, and vendor relationships to tailor personalized simulations. BEC and VEC threats thrive on the trust you’ve already built with your team and partners. They often contain no links or attachments, relying instead on contextual manipulation. Using PeopleBase and VendorBase relationship data, AI Phishing Coach now builds text-only simulations that mirror manager, colleague, and vendor interactions. Abnormal then triggers just-in-time coaching when users engage in simulated social-engineering scenarios.
Phishing Risk Scoring and BEC/VEC Simulations are Generally Available for all AI Phishing Coach customers today.
Evolving the Future of Behavioral Security
This launch marks the beginning of a new era for Abnormal. Near-term development is focused on expanding Attune's training scale, introducing derivative models for specialized use cases, and extending behavioral intelligence into additional surfaces. Future capabilities will deepen identity understanding, refine communication credibility scoring, and enable workflow analysis that reveals how attackers move through organizational processes.
The threat landscape will continue to shift. Attackers will refine their use of generative AI to craft increasingly convincing impersonations. New communication channels will create new surfaces for social engineering.
Abnormal will help our customers face these challenges head-on with coordinated capability expansions that leverage shared intelligence. As communication evolves, as threats advance, and as organizational complexity increases, the platform's intelligence layer is designed to evolve with them, applying that intelligence consistently across an expanding platform.
Attune 1.0 establishes the foundation. Enhanced cloud email security demonstrates what explainable AI and precise control can look like when built on behavioral intelligence. AI Phishing Coach shows how real-time, automated human risk management can close the loop between detection and defense.
See Abnormal in Action
Eight years ago, we made a bet: that knowing normal would prove more durable than memorizing bad. That bet is paying off. Attune 1.0 is the clearest expression of it yet—a behavioral foundation model that stops more attacks and generates less noise.
Near-term, we're focused on expanding Attune's training scale, deepening identity understanding, and extending behavioral intelligence to new surfaces.
The platform will keep evolving. The attacks will too. That's the nature of this problem, and it's why we built Abnormal the way we did.
If you're headed to RSAC 2026, come see us.
If you'd rather see what we're finding in your environment today, request a demo.
Either way, I can’t wait to show you what’s next.
1 Based on internal Abnormal data.
Disclaimer: The following is intended to outline our general product direction. It is intended for information purposes only, and may not be incorporated into any contract. It is not a commitment to deliver any material, code, or functionality, and should not be relied upon in making purchasing decisions. The development, release, and timing of any features or functionality described for Abnormal AI’s products remains at the sole discretion of Abnormal AI and is subject to change.
Related Posts
Get the Latest Email Security Insights
Subscribe to our newsletter to receive updates on the latest attacks and new trends in the email threat landscape.